Technology
CAR Tech provides secure, high-performance remote access to your applications. Our stack is built around three elements:
CAR Proxy Manager
Reverse proxy and tunnels; RDP and traffic handled without exposing your network.
No Open Ports
Ports are never opened on your network—only on our relay when needed.
CAR Tech Firewall
When ports are used, only whitelisted IPs can connect.
How Remote Connections Work
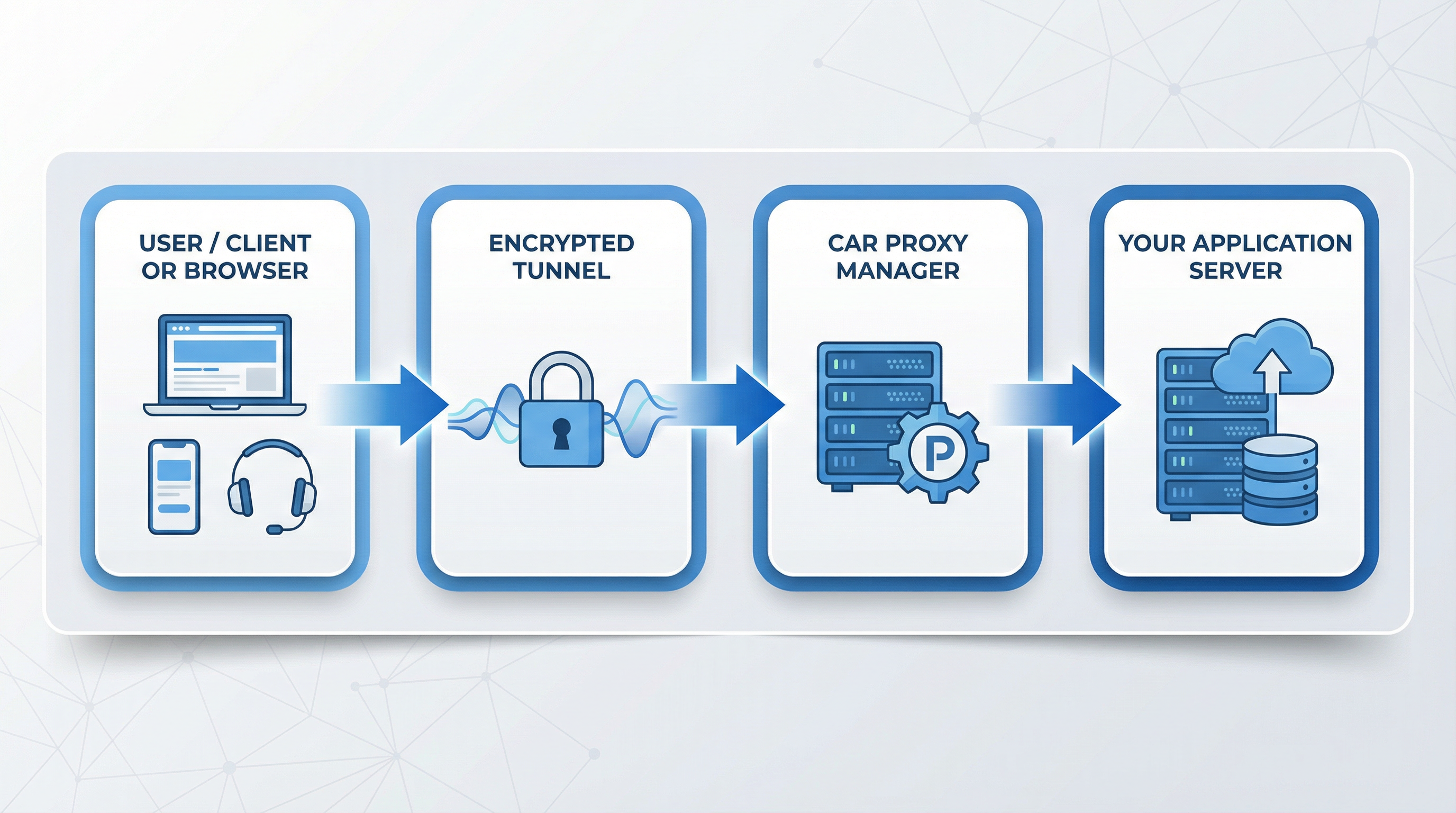
Users connect via our lightweight client or HTML5 browser. Traffic is encrypted, sent through our managed proxy layer, and forwarded to your application server—giving you centralized control and minimal latency without opening ports on your network.
If any ports are used, they are only on our relay server, never on yours; we then relay access securely to your network. For RDP we use STCP (Secret TCP) in CAR Proxy Manager, so RDP works with no ports opened on your side. When we do open ports on the relay (e.g. for RDP), CAR Tech Firewall allows only connections from whitelisted IPs.
CAR Proxy Manager
CAR Proxy Manager is our reverse-proxy and tunnel layer: it handles RDP and other traffic without exposing your network. Built for enterprise use, it integrates with CAR Software and supports application virtualization and multi-tenant access.
Capabilities:
- TCP and UDP forwarding; HTTP/HTTPS virtual hosting
- Encryption and compression; flexible routing
CAR Tech Firewall
When ports are opened on the relay server, CAR Tech Firewall limits access to whitelisted IPs only, so those ports are never open to the whole internet.
What you can do:
- Whitelist your own IP(s) via the web dashboard to connect from office, home, or other locations
- View connection status and manage your IPs (add, remove, name) in one place
- Access only the ports allowed for your account
- Optional geo-restriction: whitelist only IPs from allowed countries when enabled
Technology at a Glance
No open ports on your network
Reverse proxy and STCP; when ports are used, only on our relay, with firewall whitelist.
Security-first
Encrypted, tunneled sessions; minimal attack surface; suitable for high-security and regulated environments.
Browser access with SSL
Web sessions use SSL/TLS; traffic is protected end-to-end on desktop and in the browser.
